Cybersecurity Crisis 2026 Hits 50M Android Users and More
“`html
Cybersecurity Crisis 2026 Hits 50M Android Users and More
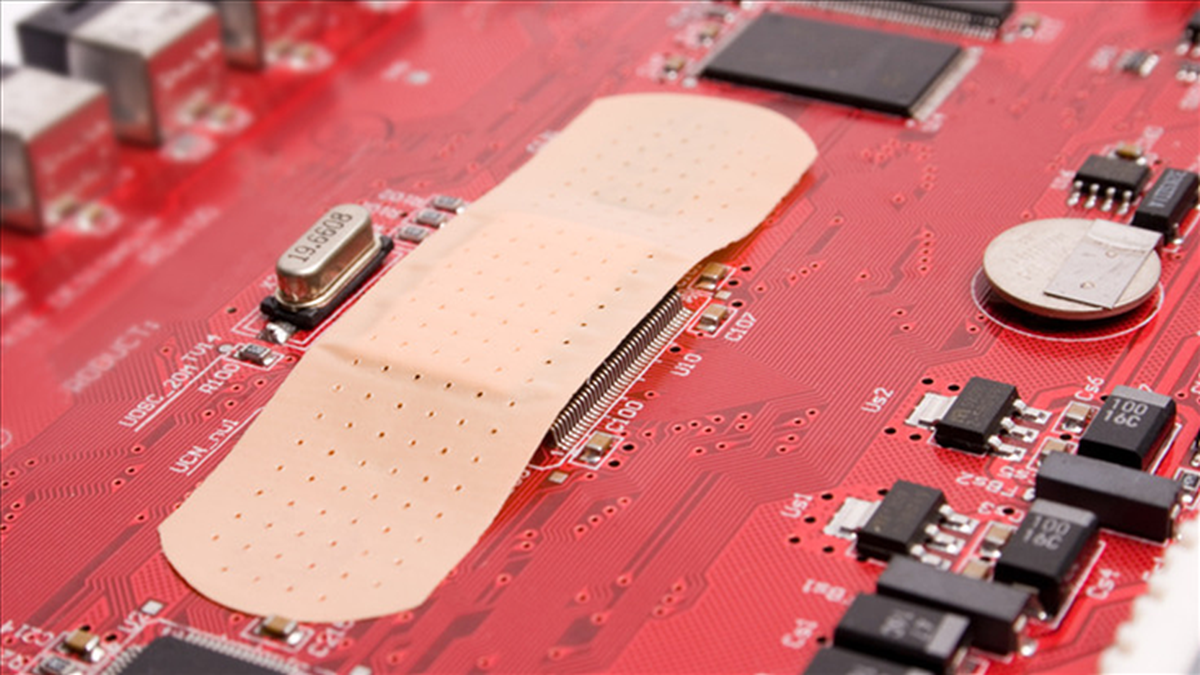
The cybersecurity world is bleeding right now. A single SDK flaw exposed 50 million Android users and 30 million crypto wallets, according to security researchers tracking the EngageLab vulnerability. Nation-states are hitting water systems, power grids, and telecoms. And the industry’s answer? A buying spree that won’t save your data tomorrow.
Why This Week Is Different
Most weeks in cybersecurity look the same. A breach here, a patch there. This week is not that. Fortinet issued an emergency hotfix on April 6, 2026, for a critical zero-day flaw in FortiClient EMS, according to threat intelligence reports. Citrix NetScaler is already under attack in what researchers say could rival the 2023 CitrixBleed crisis, one of the worst VPN exploitation events in recent memory. Signature Healthcare in Massachusetts diverted ambulances because of a cyberattack. Actual ambulances. People’s lives were at risk because someone didn’t patch a server. I don’t know how to make that more serious than it already is.
Meanwhile, Google warned on April 9, 2026, that a threat group called UNC6783 is running social engineering attacks against business process outsourcers, or BPOs, to steal corporate data and AI platform keys, according to Google’s threat intelligence team. These aren’t random hackers. This is a coordinated group linked to campaigns targeting the companies that handle your company’s customer service, HR, and back-office work.
The Bigger Picture Nobody Wants to Talk About
Here’s what I think most security reporters get wrong. They treat each breach as a separate event. They’re not. They’re symptoms of the same disease: organizations still trusting the wrong things.
Take VPNs. According to Zscaler’s 2026 VPN Risk Report, AI has collapsed human response times so much that remote access is now the fastest breach path into any organization. VPNs were supposed to be the answer to remote work security. They became the front door for attackers. That’s not bad luck. That’s a structural failure that executives ignored for years because it was cheaper to keep the old system running.
Now look at the Android situation. The EngageLab SDK flaw didn’t just affect one app. It sat inside the software development kit that dozens of apps used, exposing 50 million Android users and 30 million crypto wallets in one shot, according to security researchers. One flaw, one SDK, catastrophic reach. This is the supply chain problem that experts have warned about since the SolarWinds attack in 2020. We still haven’t fixed the incentive structure that lets bad code ship inside trusted software.
The nation-state angle makes all of this worse. Iran-linked hackers are targeting US water and energy infrastructure, according to a joint alert from the FBI and CISA. China-linked actors planted a Linux backdoor inside telecom networks to spy on government agencies and infrastructure operators. Russia’s fingerprints are on grid-probing activity being monitored by NERC. This isn’t espionage as a side project. This is preparation. These groups are mapping systems they plan to switch off someday.
And while all of this is happening, the industry is doing deals. There were 38 cybersecurity mergers and acquisitions in March 2026 alone, according to industry tracking data, following 42 deals in February 2026. Google acquired Wiz. OpenAI is buying AI security startup Promptfoo. Zurich is acquiring Beazley for $11 billion in a bet on cyber insurance. I’m not against M&A. But consolidation doesn’t patch a zero-day. It doesn’t stop UNC6783 from calling your help desk and tricking a contractor into handing over credentials.
The AI angle cuts both ways too. Yes, defenders are using AI. But malware campaigns are now blending AI with ClickFix techniques to evade detection, according to threat researchers. At RSAC 2026, researchers showed that Apple Intelligence guardrails could be bypassed using Neural Exec and Unicode manipulation. The same AI tools companies are buying to protect themselves are being used to attack them. If you’re a regular person with an Android phone or a small business owner with remote workers, the threat is real and it’s aimed at you. Running something like TotalAV antivirus protection on your devices isn’t a silver bullet, but it adds a detection layer that most people skip entirely.
What This Means for You
I’ll tell you what I would do right now if I ran a small or mid-sized business.
First, I’d audit every third-party vendor that touches my customer data. The Hims and Hers telehealth breach didn’t come from their own systems. It came through a third-party customer service platform, according to breach reports. The attackers didn’t need to break down the front door. They walked in through a side entrance that Hims and Hers left open for a vendor.
Second, I’d stop treating VPNs as a complete security solution. The Zscaler report makes it clear: VPNs are a liability in 2026, not a shield. Zero-trust access models aren’t perfect, but they’re a much better bet than trusting anyone who connects with the right password.
Third, if you have remote workers or a help desk, train them on social engineering now. UNC6783’s playbook is not technically sophisticated. They call your help desk. They pretend to be an employee. They get credentials. That’s it. Human error is the product, not the bug, in their attack chain.
Fourth, for personal devices and home offices, don’t ignore endpoint protection. Norton security suite covers multiple devices and includes identity monitoring features that matter when 30 million crypto wallets just got exposed in a single SDK flaw.
Fifth, if you hold any crypto, move it off exchange wallets and into cold storage. The Bitcoin Depot heist that cost $3.6 million is a reminder that hot wallets are targets. They always have been.
The Bottom Line
The cybersecurity industry will close hundreds of M&A deals in 2026 and write billions in insurance policies. None of that will matter if you’re still running unpatched VPNs, trusting third-party vendors blindly, and ignoring social engineering. The attacks are faster now. The attackers are better funded. Your window to get serious is closing. Stop waiting for someone else to fix this.
Frequently Asked Questions
What is the biggest cybersecurity threat right now in 2026?
Nation-state attacks on critical infrastructure and AI-assisted malware campaigns are the most serious threats in 2026. According to Google’s threat intelligence team, groups like UNC6783 are actively targeting business process outsourcers using social engineering to steal corporate data and AI platform credentials.
How did the EngageLab SDK flaw affect Android users?
The EngageLab SDK flaw was embedded in multiple Android apps, exposing 50 million users and 30 million crypto wallets in one event, according to security researchers. This is a supply chain attack, meaning users had no way to know the apps they trusted contained vulnerable code.
Is cybersecurity M&A actually making people safer?
I’d argue no, not in the short term. There were 38 cybersecurity M&A deals in March 2026 alone, according to industry tracking data, but acquisitions take time to integrate and zero-days don’t wait for deal closings. Consolidation benefits investors more than it benefits defenders right now.
What should regular people do about cybersecurity in 2026?
Update your devices immediately, especially Android phones given the EngageLab SDK exposure. Use endpoint protection on all devices, audit what apps have access to your financial accounts, and store crypto in cold wallets if you hold any meaningful amount.
Why are VPNs considered a security risk in 2026?
According to Zscaler’s 2026 VPN Risk Report, AI has accelerated breach timelines so much that remote access through VPNs is now the fastest path into an organization. VPNs authenticate users but don’t continuously verify behavior, making them easy to exploit once credentials are stolen.
“`
Get stories like this in your inbox. Daily.
Free. No spam. The AI, tech, and finance stories that move money.